Cybersecurity isn’t what it used to be. The game has completely changed. Attackers are smarter, faster, and use incredibly creative ways to break through defenses. As we look towards 2025, the threats facing your business are more sophisticated and dangerous than ever before.
Simply keeping up isn’t enough anymore. You have to stay ahead. The old playbook of just having a firewall and antivirus is obsolete. Today’s digital world demands a proactive, intelligent defense strategy. Knowing what’s coming is your first, and most important, line of defense. This guide breaks down the top cybersecurity threats of 2025 that every business leader must understand and prepare for.
Threat #1: AI-Powered Cyberattacks
Artificial intelligence is a powerful business tool. Unfortunately, criminals know this too. They are now using AI to create devastatingly effective attacks that bypass traditional security with ease.
Hackers use AI to automate their attacks on a massive scale. They can find vulnerabilities in your network faster than any human could. But the real danger lies in their social engineering tactics. Imagine a phishing email with perfect grammar, written in the exact tone of your CFO. Or a phone call that uses a perfect clone of your CEO’s voice to request an urgent wire transfer. This is the reality of AI-powered attacks. These deepfake scams are incredibly convincing and designed to trick even your most cautious employees.
The only way to fight back against malicious AI is with smarter, defensive AI. You need solutions that can analyze behavior, detect anomalies, and identify sophisticated threats in real-time. This is no longer science fiction; it’s a fundamental requirement for business cybersecurity.
Threat #2: Ransomware Evolution
Ransomware is still one of the biggest threats out there, but it has evolved into something far more sinister. Hackers are no longer content with just locking your files. They’ve adopted brutal new tactics.
It starts with “double extortion.” First, they quietly steal your sensitive data. Then, they launch the ransomware to encrypt your entire network. If you refuse to pay the ransom, they threaten to leak your confidential files online. This could be anything from customer lists to financial records. The damage to your reputation can be catastrophic.
Now, we’re seeing “triple extortion.” After they’ve stolen your data and locked your systems, they attack your customers or partners directly, blaming you for the data breach. The growth of Ransomware-as-a-Service (RaaS) means any amateur criminal can now buy a sophisticated ransomware kit on the dark web. This makes ransomware protection a critical priority for everyone, especially those in critical infrastructure and supply chains.
Threat #3: Cloud Security Vulnerabilities
Moving to the cloud offers incredible flexibility and efficiency. But it also creates new security challenges that many businesses overlook. The biggest risk isn’t the cloud provider; it’s how you use their services.
A simple misconfiguration can leave a massive security hole. Think of it as leaving the digital back door to your office wide open. Hackers are constantly scanning for these misconfigured cloud environments. Once they find an opening, they can hijack accounts, steal credentials, and access your most valuable data.
Effective cloud security isn’t a one-time setup. It requires continuous monitoring and expert management. You have to know who is accessing your data and ensure every setting is perfectly configured for maximum security. Without this diligence, your cloud platform can quickly become your biggest liability.
Threat #4: IoT and Smart Device Exploits
Look around your office. How many devices are connected to the internet? Security cameras, smart thermostats, printers, even the smart coffee machine. Each one of these Internet of Things (IoT) devices is a potential entry point for an attacker.
Manufacturers often rush these devices to market with weak or non-existent security features. Many still use factory-default passwords that are easy to guess. Hackers know this. They exploit these weak points to get a foothold in your network. From there, they can move to more critical systems.
Worse, they can group thousands of these hijacked devices into a “botnet”—a giant zombie army. They then use this botnet to launch massive Distributed Denial-of-Service (DDoS) attacks to crash your website or servers. Securing your IoT security ecosystem is no longer optional.
Threat #5: Social Engineering and Phishing 2.0
Your technology is only half the battle. Your biggest and most unpredictable vulnerability is often your people. Social engineering attacks are designed to manipulate human psychology, and they are becoming alarmingly sophisticated.
We’re not talking about spam emails with obvious spelling mistakes anymore. These are the latest cyber threats delivered through carefully crafted messages. They create a sense of urgency, fear, or authority to trick employees into clicking malicious links or revealing sensitive information. Business Email Compromise (BEC) attacks, where a hacker impersonates a senior executive, cost companies billions each year.
The best defense is a combination of advanced email security filters and continuous employee training. Your team must be your human firewall, trained to spot the red flags of a modern phishing campaign. Phishing prevention is a critical layer of any serious security strategy.
Threat #6: Supply Chain Attacks
You might have perfect security, but what about your vendors? Your business relies on a network of third-party suppliers for software and services. If one of them gets compromised, you get compromised too. This is a supply chain attack.
Hackers target a less secure vendor to get access to all of their clients. They might hide malicious code in a routine software update that your team installs without a second thought. Once inside, the code activates and gives the attackers full access to your network.
The effects are devastating because the attack comes from a trusted source, making it almost impossible to detect with traditional tools. This is why vendor risk management is so important. You have to scrutinize the security practices of every partner in your supply chain. One weak link can put your entire business at risk.
Protecting Your Business: A Comprehensive Cybersecurity Approach
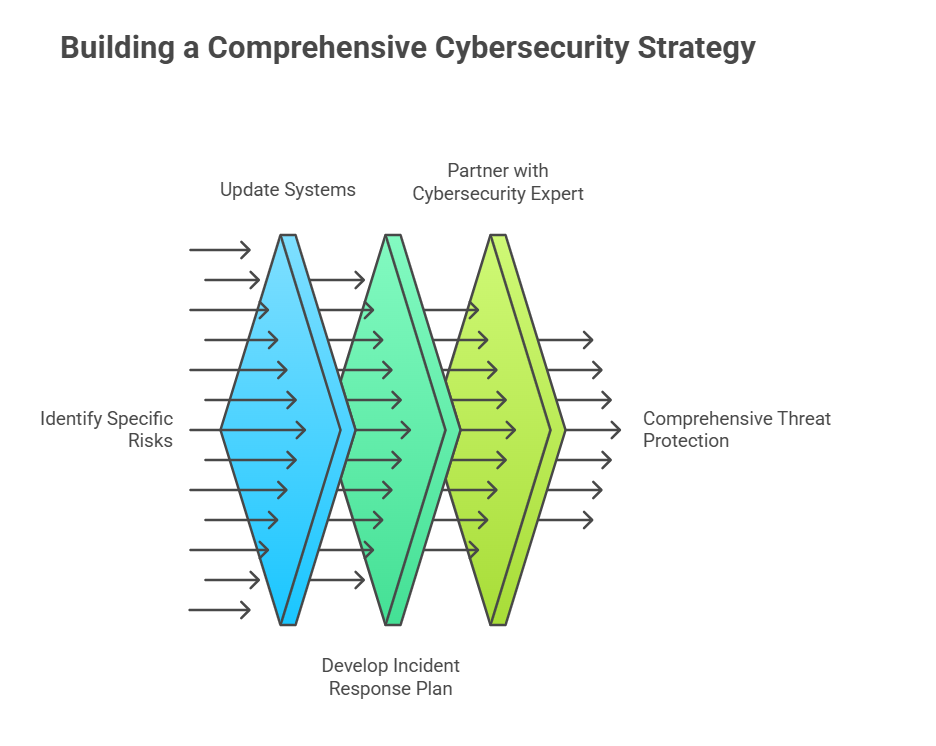
Reacting to threats is a losing battle. To truly protect your business in 2025, you need a proactive, multi-layered defense strategy. You can’t just plug one hole; you need a comprehensive shield that covers every potential vulnerability, from your cloud servers to your employees’ inboxes.
This starts with regular, professional security assessments to understand your specific risks. You need to constantly update your systems and defenses to keep pace with the attackers. Crucially, you need a rock-solid incident response plan. When an attack happens, you must know exactly what to do to minimize the damage and recover quickly.
Building and maintaining this level of security is a full-time job. Partnering with a dedicated cybersecurity expert is the most effective way to protect your business. At AILogix, we don’t just sell security products. We provide a complete threat protection service. We stay ahead of the evolving threat landscape so you can focus on running your business, confident that you are protected by a team of experts using the most advanced security solutions available.
Frequently Asked Questions
What’s the biggest cybersecurity threat to a small business?
For most small businesses, the single biggest threat isn’t a complex technical hack. It’s people. Specifically, it’s phishing and social engineering. These attacks are designed to trick your employees into giving away the keys to your kingdom. Hackers know it’s often easier to fool a person than to break through a strong firewall. One wrong click on a malicious link can bypass all your technical defenses and lead to a devastating ransomware infection or data breach.
How can I protect my business without a large IT security team?
That’s a challenge for many businesses. You can’t afford a dedicated, in-house security team. The smartest and most cost-effective approach is to partner with a Managed Security Service Provider (MSSP). Think of it like having an entire team of cybersecurity experts on call, for a fraction of the cost of hiring even one. An MSSP like AILogix handles the 24/7 monitoring, threat detection, and system updates for you, giving you enterprise-grade protection that fits your budget.
Is my business really a target for sophisticated cyberattacks?
This is a dangerous misconception. The answer is yes, you are a target. Hackers don’t pick targets one by one anymore. They use automated tools to scan thousands of businesses at once, looking for any weakness. They often see smaller businesses as easier targets because they assume you have weaker defenses. Your data is valuable, no matter your size, and you are absolutely on their radar.
What is the first step a business should take to improve its security?
The absolute first step is to understand your risks. You need a professional security assessment. You wouldn’t build a house without a blueprint, and you shouldn’t build a defense without knowing where your weak points are. A thorough assessment will identify your vulnerabilities—whether in your technology, your processes, or your employee training—and give you a clear, prioritized roadmap for what to fix first.
How does a comprehensive security approach from AILogix differ from just using antivirus software?
That’s a great question. It’s like comparing a simple lock on your front door to a complete security system with cameras, alarms, and a 24/7 monitoring service. Antivirus is a single, essential tool that protects against known viruses. It’s reactive. A comprehensive security approach from AILogix is proactive. We manage your firewall, monitor your network for suspicious activity, train your employees, and plan your response for when an attack happens. It’s a complete shield designed to protect your entire business, not just a single piece of armor.